
As anyone involved in the video workflow development process might tell you, getting high-quality content to prospective consumers is not an easy build and requires many input factors. Some of the oft-overlooked and possibly more complex factors are the content protection measures that ensure the video isn’t being pirated. According to our 2020 Video Developer Report, 33% of respondents don’t use any DRM Security and Protection measures, while an impressive 22% indicated that they’ve built their very own in-house solutions.
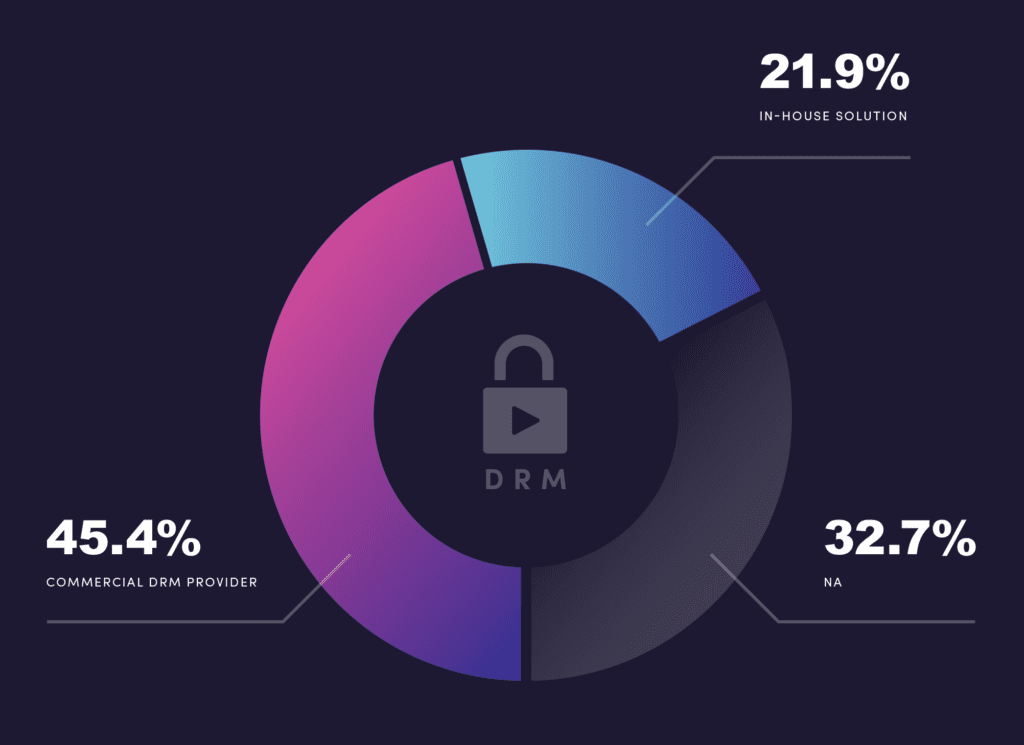
Given that 55% of respondents don’t use any kind of DRM or have taken on the challenge of implementing their own content security measures, we wanted to help ease (or improve) the understanding of the types of measures an organization can apply and how to do so. For this, Bitmovin brought in some of the video streaming industry’s leading experts in Digital Rights Management for a brand new virtual event series: DRM Security and Protection Week. During this series, Bitmovin was joined by BuyDRM, EZDRM, Intertrust, Irdeto, Vualto & Axinom as they covered topics like Heartbeat Monitoring, Multi-DRM implementations in the cloud, Watermarking, and more. In case you missed any of these sessions for any reason, we’ve put together this blog post to summarize the presentations with some high-level takeaways.
Intertrust: Reduce TCO with Direct-to-TV broadcasting using DRM-based converged security
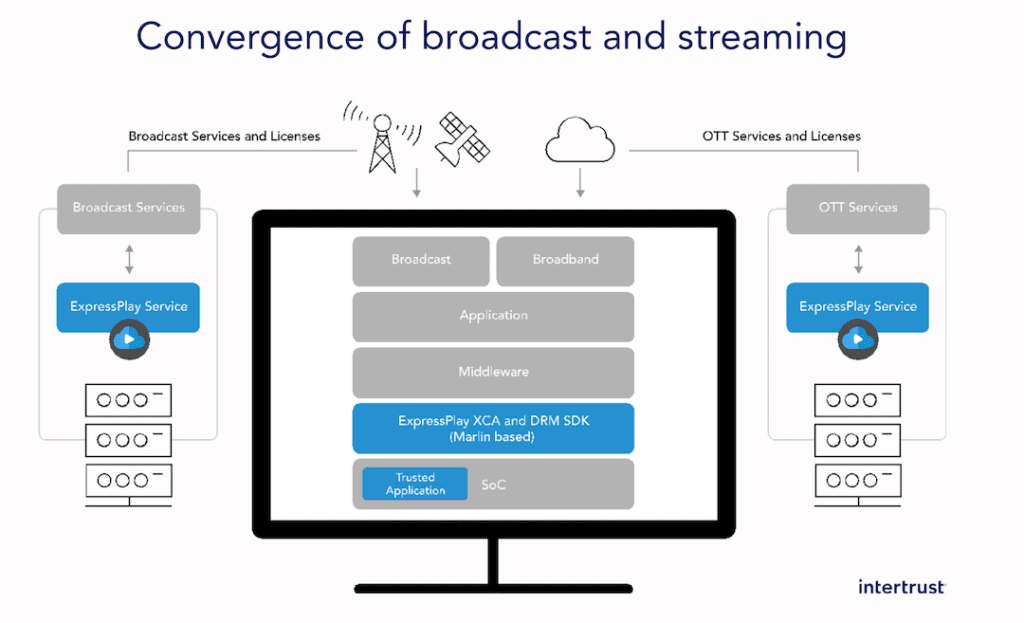
Intertrust kicked off the DRM security and protection week by defining how DRM converged security can bridge the digital gap and support direct-to-TV broadcasting and OTT services, all while saving on the total cost of ownership with a cloud-based network-agnostic infrastructure that can communicate with both a classic conditional access system (CAS) and the digitally-oriented DRM solution.
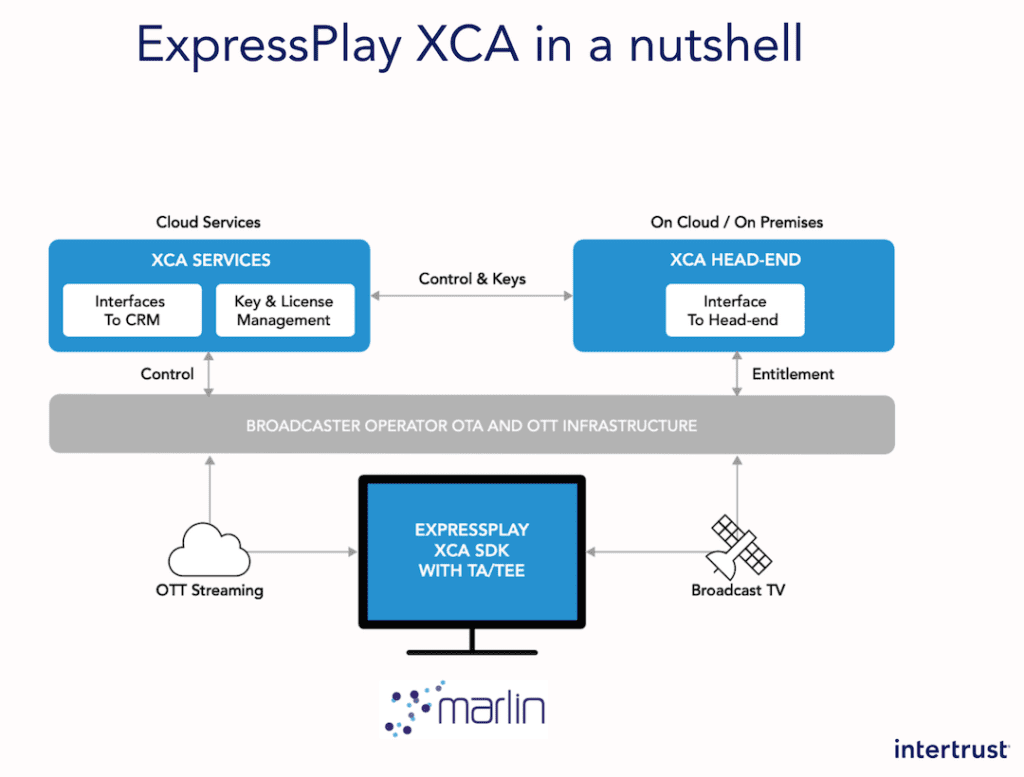
Intertrust’s ExpressPlay XCA (built on and supported by MarlinDRM) offers this middleware solution by running an operator app that’s enabled by almost all major set-top boxes (STBs), smart cards, and conditional access modules (CAMs)
BuyDRM – Deploying Multi-DRM for CMAF
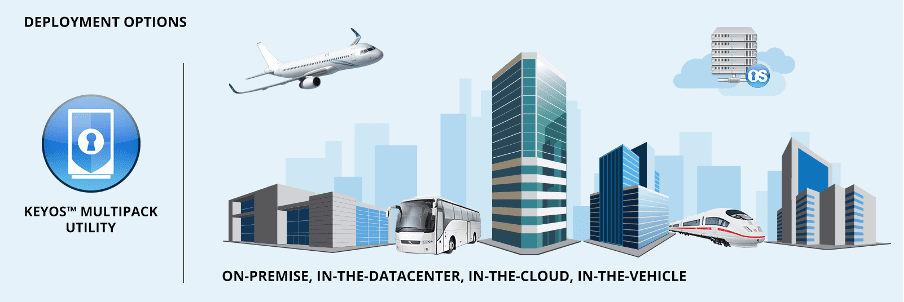
BuyDRM followed up by discussing the specific processes that go into implementing a dynamic DRM solution to keep up with the ever-evolving Common Media Application Format. BuyDRM supports CMAF across their platform from encryption to license delivery and just announced new support for CMAF in their MultiPack Utility and MultiPack plug-in for Wowza.
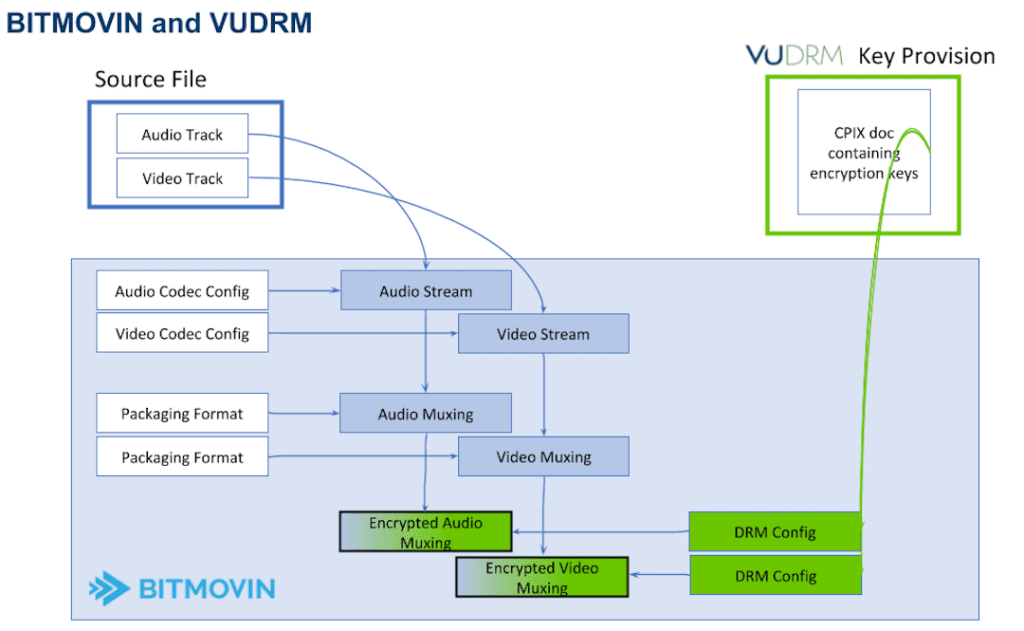
DRM Complexities Untangled: VUALTO and Bitmovin demo CBCS encrypted CMAF with VUDRM
For those with limited DRM knowledge or seeking to learn how to two to knock out two birds with one stone with an integrated encoding and content protection system Bitmovin teamed up with VUALTO to display how an organization can implement a CBCS encryption with VUDRM. This session demonstrated how a team would go about building this system with geo-restrictive and concurrency token code samples and case studies.
Irdeto: Concurrent Stream Management at Scale
Perhaps the biggest elephant in the DRM security and protection conversation is account sharing by end-users. Although most streaming organizations would naturally prefer that one account = one stream, the reality is that this model is often very off-putting for consumers who have multiple individuals in a household or would prefer to share an account. The middle-ground solution is to limit users who can stream at one time, otherwise known as concurrency management. However, once an organization reaches a certain scale, managing concurrency can become a challenging endeavor. Irdeto and Bitmovin teamed up to discuss how a streaming organization can gain and retain control over who is viewing the content in a fast, simple, and smart way.
Learn how you can apply concurrency management, what challenges you may face, and what the cost of failing to control stream management will have on your bottom-line in this high-level discussion.
EZDRM: How to implement DRM in 30 mins or less
DRM implementation doesn’t have to be complex or require countless hours to implement into your existing workflow. In this session, Bitmovin and EZDRM came together to discuss the very basics, defining exactly what is Digital Rights Management, why you need it, and how you can set it up in 30 minutes or less using native browser DRMs and SDKs and out-of-box encoding solutions.

Axinom: Mastering DRM license and client configuration in a multi-DRM world
To close out the DRM security and protection week, the content delivery and DRM organization, Axinom explained the license configuration process for Widevine, Fairplay, and PlayReady using Axinom DRM. In this demonstration, Axinom proposed the concept of Entitlement Message codes, which are produced at runtime by the customer backend using a simple JSON structure to display how content can be securely delivered to nearly any player device or service. This method creates a singular DRM tech-agnostic authorization mechanism that’s embedded in a signed JSON Web Token (JWT).
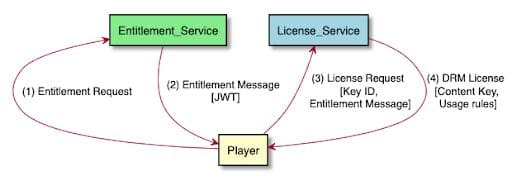 This process can be seen in a full end-to-end delivery worfklow below:
This process can be seen in a full end-to-end delivery worfklow below:

With a few real-life cases, the session displayed how to configure your content protection workflow to handle up to 100,000 DRM requests/second with varying levels of security, license persistence, and multi-key delivery methods.
DRM Security and Protection – How it all Fits
Much like all systems in video workflow, there is rarely a one-size-fits-all solution for any streaming organization. This equally applies to content protection which requires completely different solutions for different needs, from broadcasters to start-ups, to mid-size OTTs, to those who are simply looking to build their process for scale fast, and at an affordable cost. If you’d like to view all of these sessions to understand which solution fits your organization best, check out the full line-up sessions here.
Did you like this post? Check out some of our other great content below:
- [PDF Whitepaper] State of the Web: Digital Rights Management
- [Blog post] Digital Rights Management (DRM) – Everything you need to know
- [Blog post] Guide to Selecting and Implementing DRM & Content Protection
- [Content Series] How to Trust Your Player



